


- Optics Overview
- Night Vision Overview
- Telescope Accessories
- Astrophotography Site
- Dwarf II AI Telescope Classic
- Dwarf II AI Telescope Deluxe
- SeeStar S50
- SarBlue Mak60 Telescope
- GoSky 20-60x80 Spotting Scope
- Gosky 20-60x80 ED Ultra HD
- GoSky 20-60x80 Waterproof
- GoSky 12x55 Monocular
- GoSky SmartPhone Adaptors
- GoSky Eagleview ED 10x42
- GoSky 10x42 Binoculars
- Night Vision NV400
- Night Vision DT49 4K Binocular
- Night Vision DT18 Monocular
- Night Vision DT19 Monocular
- Night Vision DT29 Binocular
- Night Vision DT39 Binocular
- Night Vision DT88 Binocular
- Night Vision DT99 Binocular
- DH1 Trail Camera
- DT40 12x32 Binocular Camera
- Vehicle /Car Window Mount
- Optics Catalogue - download


- Fosi Audio Overview
- Fosi Audio BT20A
- Fosi Audio BT20A Pro Amp
- Fosi Audio BL20A
- Fosi Audio BT30D Pro
- Fosi Audio V3 Amplifier
- Fosi Audio MC351
- Fosi Audio AK170
- Fosi Audio ZK-1002D
- Fosi Audio BT30D
- Fosi Audio TB10D
- Fosi Audio T10 WiFi Amp
- Fosi Audio B2 Speaker
- Fosi Audio C4 Speaker
- Fosi Audio A5 Soundbar
- Fosi Audio K5 Pro Gaming Dac
- HDMI 4x8 Matrix Cat5e/6
- Audio Catalogue - download


- Press Releases
- Graphic Image Technologies announces the availability of DVTEL Meridian 2TB and 4TB
- Opinion Piece: 4K myths debunked
- The release of TVU One – a compact mobile All-In-One IP video transmission solution
- Quasar 4K Ultra HD Cameras from GIT take video surveillance quality to new heights
- Increasing integration capabilities are the future of commercial security solutions
- LC Sequ-door improves productivity and customer service with remote surveillance solution from GIT
- 7Arrows Security cracks down on Petervale crime with SerVision and DVTel solution from GIT
- CCTV with remote monitoring boosts security, offers additional benefits for public transport sector
- CCTV with remote monitoring is the ultimate business security and productivity tool
- DVTEL Quasar 4K Ultra HD Cameras from GIT take video surveillance quality to new heights
- GIT and Secusystems use Servision to cut illegal mining in Tanzania and Ghana by 50%
- Thermal imaging cameras can bolster anti-poaching initiatives
- GIT offers customer training on DVTel analytics solutions
- GIT offers new dvtel intelligent thermal imaging cameras with analytics
- Five rules to help you make the most of your CCTV solution
- GIT to distribute full range of dvtel solutions
- Live proactive monitoring and surveillance helps curb cash-in-transit heists
- Instantly share live video between multiple broadcast facilities with the TVU Grid from GIT
- GIT offers the full range of TVU products
- Thava Restaurant Improves service Levels with SerVision
- Video Flow for Broadcasting over the internet
- GIT Supports Olivers House
- GIT showcases innovative solutions at Mediatech
- ATM CCTV Solution
- Leveraging additional value from Video Surveillance Solutions
- Reducing Theft of Goods in Transit
- Local and Global Mining CCTV
- Lowering Risk in Businesss Parks
- Someone to watch over our children
- Supersizing remote Surveillance
- Vehicle Monitoring
- Mobile CCTV
- Retail Surveillance over Narrow band
- Remote CCTV and Holiday Homes
- 5 Common Misconceptions in CCTV
- Before you throw out analogue security cameras in favour of IP
- Case Study: Productivity Tool
- School Bus Mobile DVR Project
- Harmonic used to provide SABC SWC 2010 Video

© Graphic Image Technologies 2021


































































































































































































































































































































































































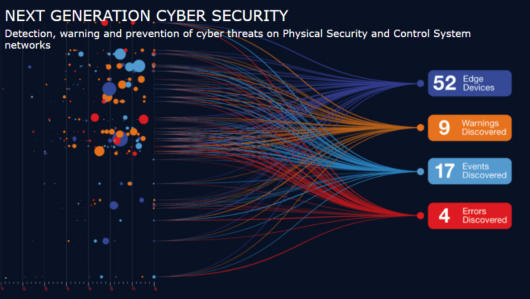
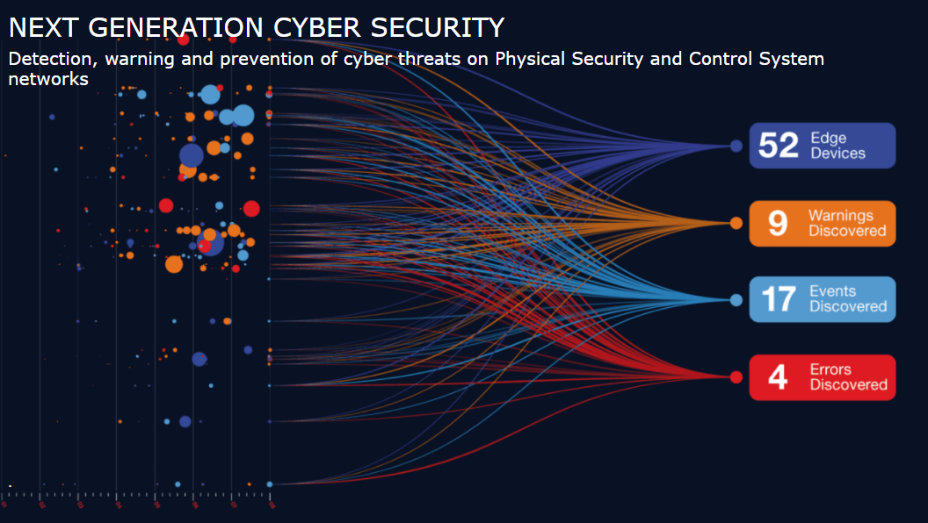
Security - Next Gen Cybersecurity Solution for BMS networks
Nelysis CyberSecurity Solutions
The demand for 24/7 cyber defense for Physical Security is ever increasing as the landscape of critical infrastructures has changed immensely. New considerations are needed to face today’s terrorist threats: the apparent randomness and the easiness of the attacks make a potential target far less obvious. Now more than ever, physical security must be active 24/7. Every risk manager of either critical infrastructure or Small Medium Business with important assets to protect, needs high physical security protection to control access to the facilities. Today’s security, safety and comfort, are increasingly dependent on the growing use of physical security and BMS systems. This growth often leads to multiple complex systems, which make it challenging to control and properly maintain, and usually require professional IT personnel. Billions of Rands are invested in physical security and BMS systems by businesses and governments to provide safety, security and service. These systems are essential to maintaining smooth operations and maintaining maximum security. CCTV, Access Control and Building Management Systems represent an Achilles heel for government and commercial enterprises whereby access to their data systems can be gained and exploited via a physical security element. Nelysis provides the next generation of protection by utilising AI and Cybersecurity techniques to protect your assets by proactively monitoring your enterprises environment. In addition to protecting your environment, the platform also provides operational insights accessible to facilities and security managers via an easy to use dashboard.
The Vanguard Network Solution
The Vanguard Network Cyber Management Software (NCM) is a unique system enabling early detection and protection of cyber threats on
Physical Security and Control Systems networks
The Vanguard Network Cyber Management Software (NCM) system visualizes the network and its various elements, detects and identifies a
wide range of cyber-threats, including new threats and 0-day exploits
The Vanguard Network Cyber Management Software (NCM) system monitors all network traffic by means of DPI Deep Packet Inspection,
detects mismatches with established behavior profiles and issues alerts
The metadata is stored in a Big Data Repository for forensic analysis
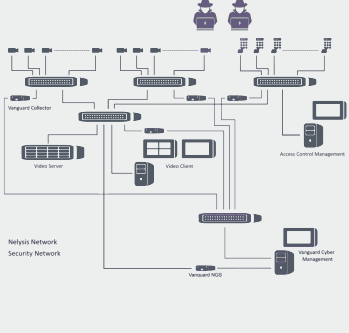



Benefits of the Architecture
Non-intrusive, full separation between the monitored network and the Cyber Protection network Active Protection, upon detection of a threat, it disconnects the communication with the malicious device Information is shared and alerts are sent to the event management system The existing communication switches are controllable for immediate protection purposes Unlimited expansion – The software architecture allows expansions as needed without limitations
Centralized management
Interactive Dashboard for network management and visualization of threats Real-time alerts are sent to the operator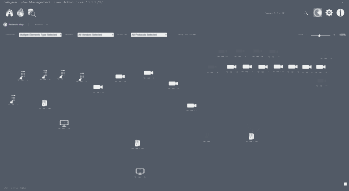

Automatic network discovery
Interactive Network mapping and visual presentation of all connected devices Analysis at layers 7 & 4Behavior Monitoring
Continuous monitoring of the network components and network traffic (DPI) Constant monitoring of element’s behavior vs approved profiles and behavior patterns Deviations of patterns behavior are immediately detected by means of Deep Learning algorithms Metadata information are saved for forensic analysis and comprehension of historical changesDetectable Cyber-Threats
• New Threats • DoS attacks • MITM (Man-In-The-Middle) • Communication with unauthorized IP • Unauthorized L7 protocols • Brute Force password attacks • Port Scanning • MAC address change/new • IP address change/new • Off line elements • Device unusual traffic • Device unusual throughput • Web Browsing • Unusual operations on endpoints




- Optics Overview
- Night Vision Overview
- Telescope Accessories
- Astrphotography Solutions
- Dwarf II AI Telescope Classic
- Dwarf II AI Telescope Deluxe
- SeeStar S50
- SarBlue Mak60 Telescope
- GoSky 20-60x80 Spotting Scope
- GoSky 20-60x80 ED HD Spotting Scope
- GoSky 20-60x80 Waterproof Scope
- Gosky 12x55 Monocular
- GoSky Smartphone Adaptor
- GoSky EagleView ED10x42
- GoSky 10x42 Binoculars
- Night Vision NV400 Binocular
- Night Vision DT49 4K Binocular
- Night Vision DT18 Monocular
- Night Vision DT19 Monocular
- Night Vision DT29 Binocular
- Night Vision DT39 Binocular
- Night Vision DT88 Binocular
- Night Vision DT99 Binocular
- DH1 Trail Cam
- DT40 12x32 Binocular Camera
- Vehicle Car Window Mount
- Optics Catalogue - download


- Fosi Audio Overview
- Fosi Audio BT20A
- Fosi Audio BL20A
- Fosi Audio BT20A Pro
- Fosi Audio MC351
- Fosi Audio V3 Amplifier
- Fosi Audio AK170
- Fosi Audio ZK-1002D
- Fosi Audio BT30D
- Fosi Audio BT30D Pro
- Fosi Audio TB10D
- Fosi Audio T10 WiFi Amp
- Fosi Audio B2 Speaker
- Fosi Audio C4 Speaker
- Fosi Audio A5 Soundbar
- Fosi Audio K5 Pro Gaming DAC
- HDMI 4x8 Matrix Cat5e/6
- Audio Catalogue


- About
- BEE Certificate
- Clients
- Press Releases
- Graphic Image Technologies announces the availability of DVTEL Meridian 2TB and 4TB
- Opinion Piece: 4K myths debunked
- The release of TVU One – a compact mobile All-In-One IP video transmission solution
- Quasar 4K Ultra HD Cameras from GIT take video surveillance quality to new heights
- Increasing integration capabilities are the future of commercial security solutions
- LC Sequ-door improves productivity and customer service with remote surveillance solution from GIT
- 7Arrows Security cracks down on Petervale crime with SerVision and DVTel solution from GIT
- CCTV with remote monitoring boosts security, offers additional benefits for public transport sector
- CCTV with remote monitoring is the ultimate business security and productivity tool
- DVTEL Quasar 4K Ultra HD Cameras from GIT take video surveillance quality to new heights
- GIT and Secusystems use Servision to cut illegal mining in Tanzania and Ghana by 50%
- Thermal imaging cameras can bolster anti-poaching initiatives
- GIT offers customer training on DVTel analytics solutions
- GIT offers new dvtel intelligent thermal imaging cameras with analytics
- Five rules to help you make the most of your CCTV solution
- GIT to distribute full range of dvtel solutions
- Live proactive monitoring and surveillance helps curb cash-in-transit heists
- Instantly share live video between multiple broadcast facilities with the TVU Grid from GIT
- GIT offers the full range of TVU products
- Thava Restaurant Improves service Levels with SerVision
- Video Flow for Broadcasting over the internet
- GIT Supports Olivers House
- GIT showcases innovative solutions at Mediatech
- ATM CCTV Solution
- Leveraging additional value from Video Surveillance Solutions
- Reducing Theft of Goods in Transit
- GIT offering reduces theft of goods in transit
- Local and Global Mining CCTV
- Lowering Risk in Businesss Parks
- Someone to watch over our children
- Supersizing remote Surveillance
- Vehicle Monitoring
- Mobile CCTV
- Retail Surveillance over Narrow band
- Remote CCTV and Holiday Homes
- 5 Common Misconceptions in CCTV
- Before you throw out analogue security cameras in favour of IP
- Case Study: Productivity Tool
- School Bus Mobile DVR Project
- Harmonic used to provide SABC SWC 2010 Video
- Section 51
© Graphic Image Technologies 2021


































































































































































































































































































































































































Security - Next Gen Cybersecurity Solution for BMS networks
Nelysis CyberSecurity Solutions
The demand for 24/7 cyber defense for Physical Security is ever increasing as the landscape of critical infrastructures has changed immensely. New considerations are needed to face today’s terrorist threats: the apparent randomness and the easiness of the attacks make a potential target far less obvious. Now more than ever, physical security must be active 24/7. Every risk manager of either critical infrastructure or Small Medium Business with important assets to protect, needs high physical security protection to control access to the facilities. Today’s security, safety and comfort, are increasingly dependent on the growing use of physical security and BMS systems. This growth often leads to multiple complex systems, which make it challenging to control and properly maintain, and usually require professional IT personnel. Billions of Rands are invested in physical security and BMS systems by businesses and governments to provide safety, security and service. These systems are essential to maintaining smooth operations and maintaining maximum security. CCTV, Access Control and Building Management Systems represent an Achilles heel for government and commercial enterprises whereby access to their data systems can be gained and exploited via a physical security element. Nelysis provides the next generation of protection by utilising AI and Cybersecurity techniques to protect your assets by proactively monitoring your enterprises environment. In addition to protecting your environment, the platform also provides operational insights accessible to facilities and security managers via an easy to use dashboard.
The Vanguard Network Solution
Vanguard Network Cyber Management Software (NCM) is a
unique system enabling early detection and protection of cyber
threats on Physical Security and Control Systems networks
The Vanguard Network Cyber Management Software (NCM)
system visualizes the network and its various elements, detects
and identifies a wide range of cyber-threats, including new
threats and 0-day exploits
The Vanguard Network Cyber Management Software (NCM)
system monitors all network traffic by means of DPI Deep Packet
Inspection, detects mismatches with established behavior
profiles and issues alerts
The metadata are stored in a Big Data Repository for forensic
analysis

Benefits of the Architecture
Non-intrusive, full separation between the monitored network and the Cyber Protection network Active Protection, upon detection of a threat, it disconnects the communication with the malicious device Information are shared and alerts are sent to the event management system The existing communication switches are controllable for immediate protection purposes Unlimited expansion – The software architecture allows expansions as needed without limitations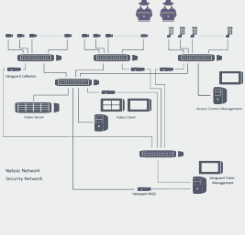

Centralized management
Interactive Dashboard for network management and visualization of threats Real-time alerts are sent to the operator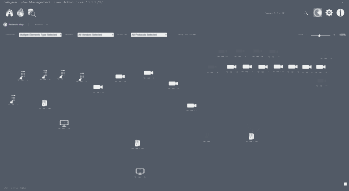
Automatic network discovery
Interactive Network mapping and visual presentation of all connected devices Analysis at layers 7 & 4
Behavior Monitoring
Continuous monitoring of the network components and network traffic (DPI) Constant monitoring of element’s behavior vs approved profiles and behavior patterns Deviations of patterns behavior are immediately detected by means of Deep Learning algorithms Metadata information are saved for forensic analysis and comprehension of historical changesDetectable Cyber-Threats
• New Threats • DoS attacks • MITM (Man-In-The-Middle) • Communication with unauthorized IP • Unauthorized L7 protocols • Brute Force password attacks • Port Scanning • MAC address change/new • IP address change/new • Off line elements • Device unusual traffic • Device unusual throughput • Web Browsing • Unusual operations on endpoints